Find a Mimecast plan that fits your needs
You’re up against difficult business challenges. Mimecast is here to help. Pick between a variety of plans and find solutions to your most challenging issues.
Email is the door through which nearly all vital business communication flows – and the one where virtually all cyberattacks begin. As ransomware, phishing, brand impersonation and malware become more advanced, your email security needs to as well. That’s where Mimecast comes in.

Legacy security solutions aren’t enough to keep up with today’s sophisticated and expanding threat landscape.

Without email authentication, anyone can spoof your brand’s domain and send malicious emails to customers and partners.

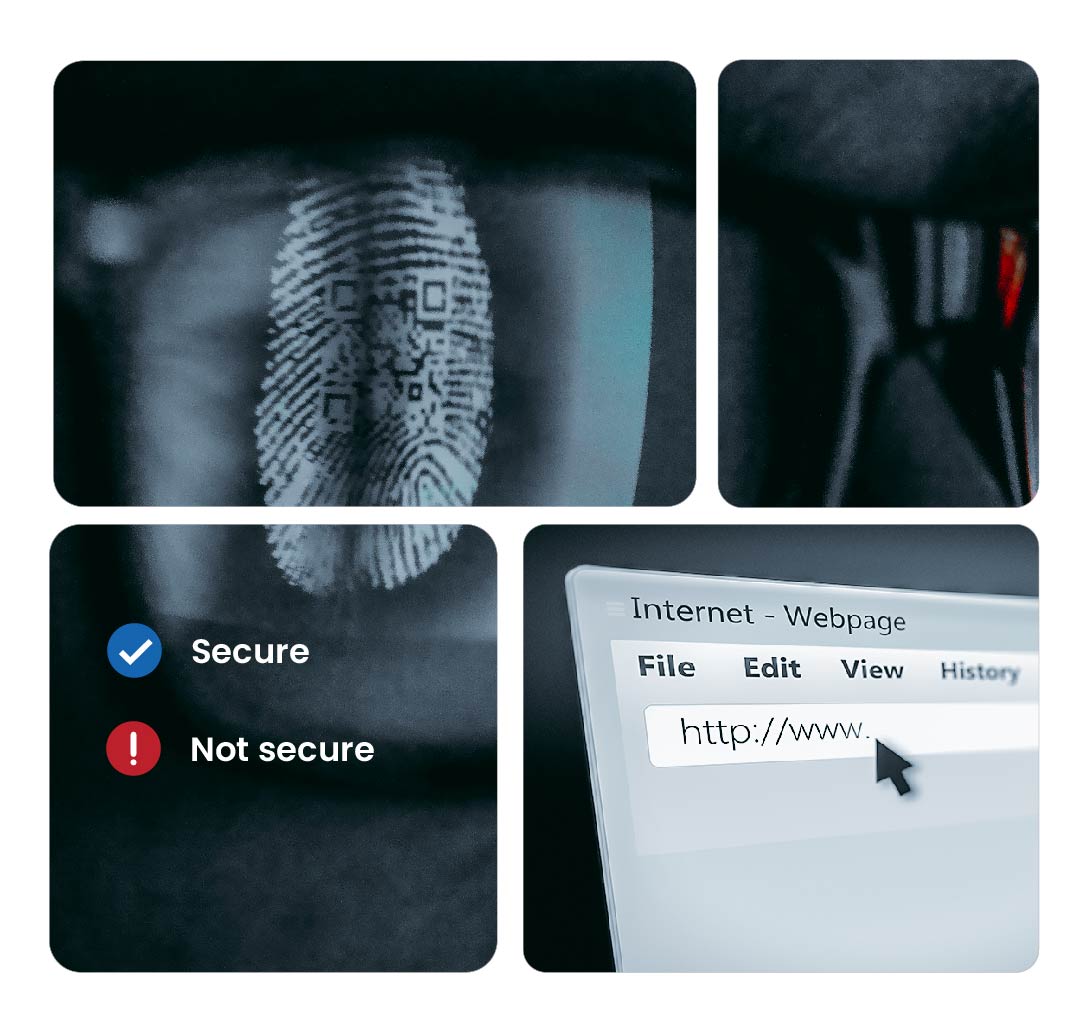
QR phishing attacks are only getting more sophisticated, which makes preventing them the best defense.
Our Advanced Email Security product improves protection with real-time threat analysis and filtering before emails get opened.

Leverage industry-leading AI to defend your employees from sophisticated social engineering and business email compromise attacks.
Mimecast DMARC Analyzer makes it easier to stop email impersonation and deter fraud that steals your good name.
Defend against threats to your expanding attack surface by protecting Microsoft Teams, SharePoint, and OneDrive.




You’re up against difficult business challenges. Mimecast is here to help. Pick between a variety of plans and find solutions to your most challenging issues.
Mimecast is proud to protect and support 42,000+ organizations globally, helping
them navigate the ever-expanding security threat landscape.




Email is cybercriminals’ method of choice for entering business networks and stealing from them; email is also most organizations’ primary means of communications. Thus, email security safeguards employee communication and reduces risk with targeted threat protection, data leak prevention, and enforced email security controls. Multiple layers of email security protection are required to stop known and emerging email-borne threats before they reach your organization’s environment.