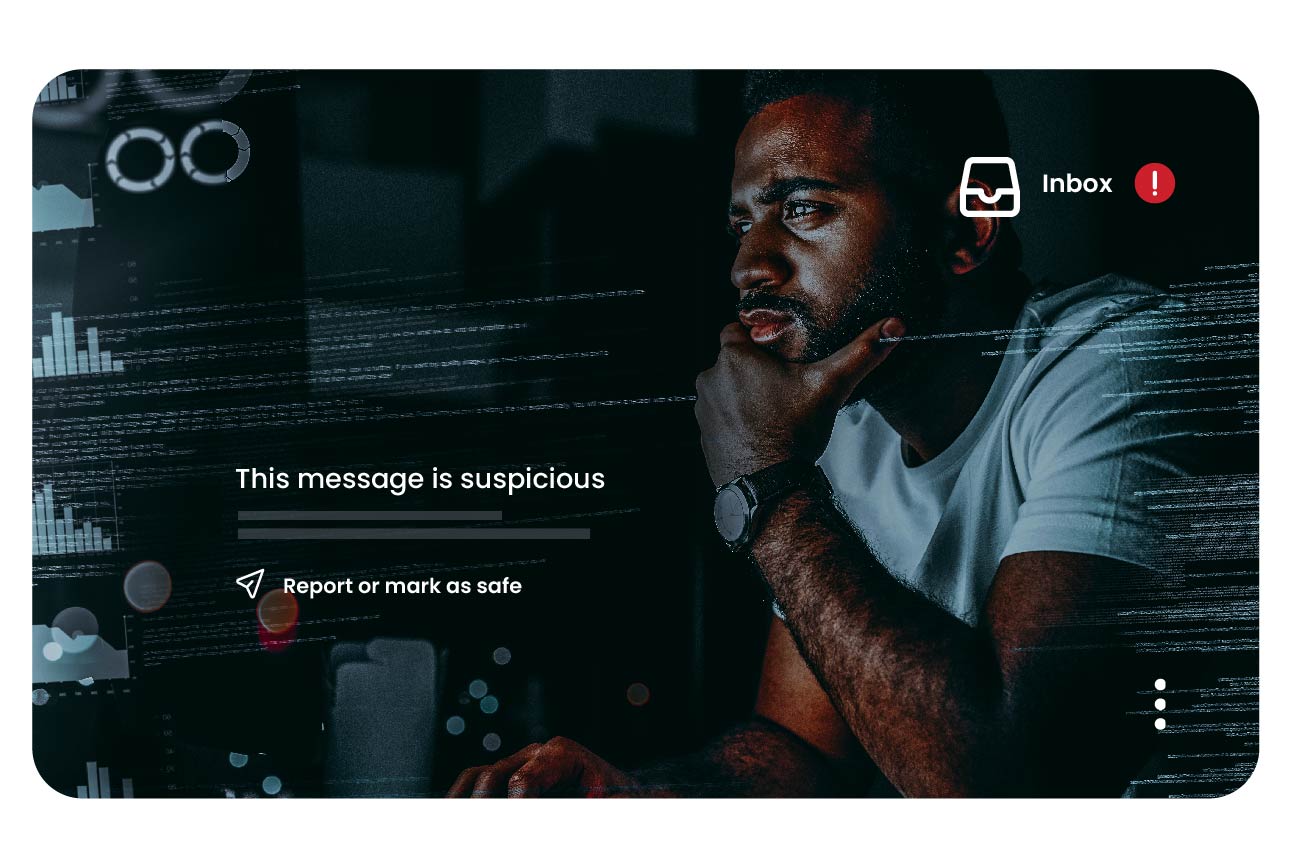
Frequently Asked Questions
Explore more details about email security.
How does Mimecast use artificial intelligence (AI)?
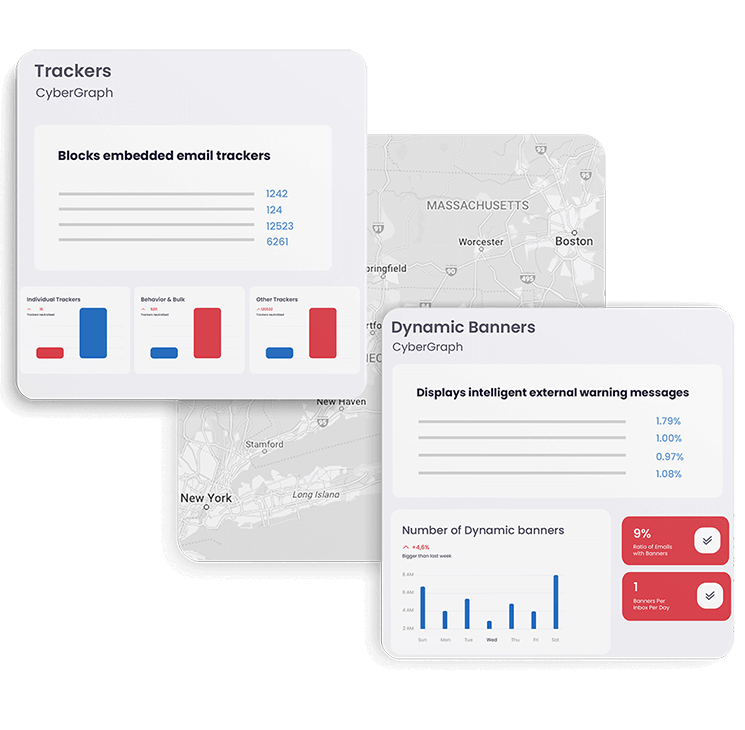
Mimecast protects customers with multiple detection engines that pairs advanced AI and machine learning with industry-leading technologies tuned and improved over the past 20 years based on trillions of emails and millions of users.
What are secure email gateways (SEGs)?
Secure Email Gateways work as a collection of different technologies that work together to block email threats. Secure Email Gateways or email gateways are an email security product or solution that sits inline on emails’ pathway from the web to the corporate email server. The gateway scans all incoming, outbound and internal email communications, including attachments and URLs for signs of malicious or harmful content.
What type of email threats do secure email gateways protect against?
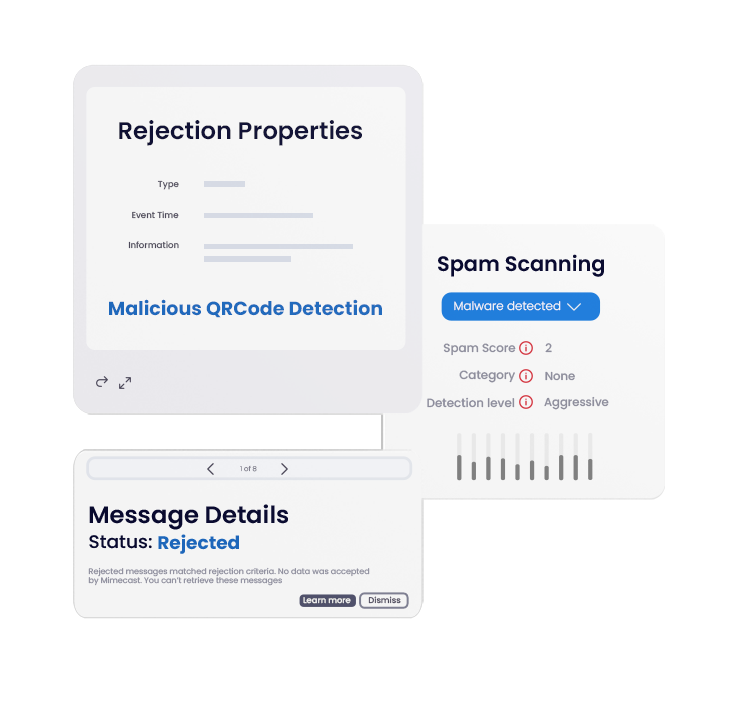
Email is the number one vector used by hackers to get access to a company’s private data, using attacks like phishing. A secure email gateway product protects businesses from spam, viruses, malware and denial of service attacks (DDoS). Email gateways also offer protection from advanced social engineering attacks such as phishing, or business email compromise.
Why are secure email gateways important for organizations?
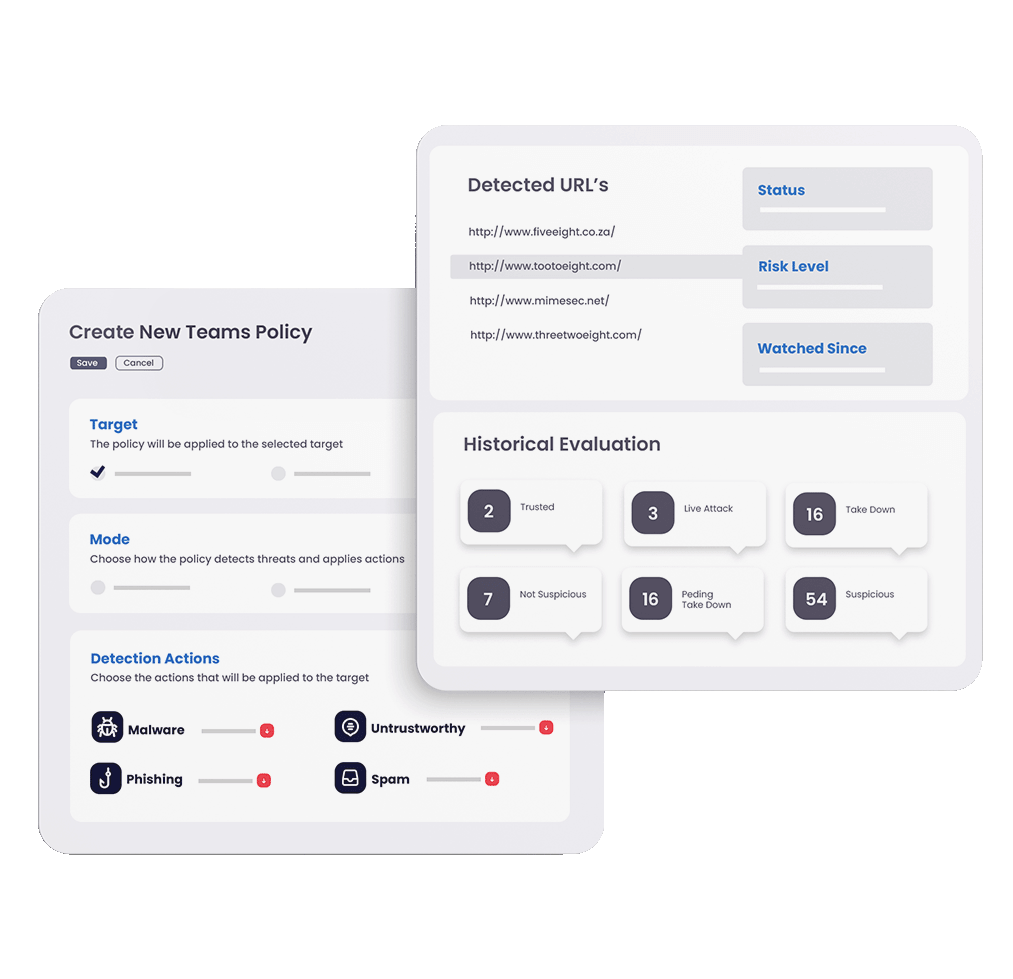
Secure Email Gateways provide pre-delivery protection by blocking email based threats before they reach a mail server, whether on-premise or on Microsoft 365 (previously Office 365) or Google Workspace (previously G-Suite). Alongside blocking incoming threats, Email Gateways will also scan outgoing content. This can help protect businesses from data loss. Email security solution providers like Mimecast will provide Email Archiving functionality, which stores emails for legal compliance and data management along with Continuity and Security Training & Awareness solutions.
How do secure email gateways work?
Secure Email Gateways act as firewalls for email and can be deployed on the cloud, on-premises or in a hybrid environments. They reroute inbound and outbound email via proxy through its own agent, which then performs a scan of the email. The scan looks at different aspects of the email to decide whether it contains threats. If so, it filters the email. Mimecast's Email Security (Gateway) filtering technology uses dynamic threat intelligence feeds to determine which emails are malicious. These feeds may include blacklisted URLs, flagged keywords, or other suspicious qualities that suggest an email may contain a security threat.
Who needs a secure email gateway?
No matter the size of an enterprise, email and collaboration mediums are a prime target for cyberattacks, and a Secure Email Gateway is a security necessity to protect your communications, people and data. Secure Email Gateways offer the most vital level of protection against malicious messages and attachments. Using a Secure Email Gateway will allow all types of organizations to enhance their security posture with greater control, policy management and customized set-up.