False Positives Continue to Dog Cybersecurity Industry
False positive security alerts will keep draining cybersecurity team resources and performance until automation is fully implemented and tightly integrated.
Key Points
- In the midst of an “alert overload,” cybersecurity professionals face a particularly acute problem of managing the deluge of false positive alerts.
- New survey data underscores the impact on sustainable security as well as staff satisfaction.
- Automation and integration in threat monitoring and protection are poised to take much of the pain out of managing alerts.
Cybersecurity’s false positive alert problem just won’t go away. Evidence continues to mount, revealing just how badly false positives are undermining companies’ IT security teams and the defenses they mount. And while innovations in threat monitoring and protection are targeting the problem, most organizations need time to roll them out.
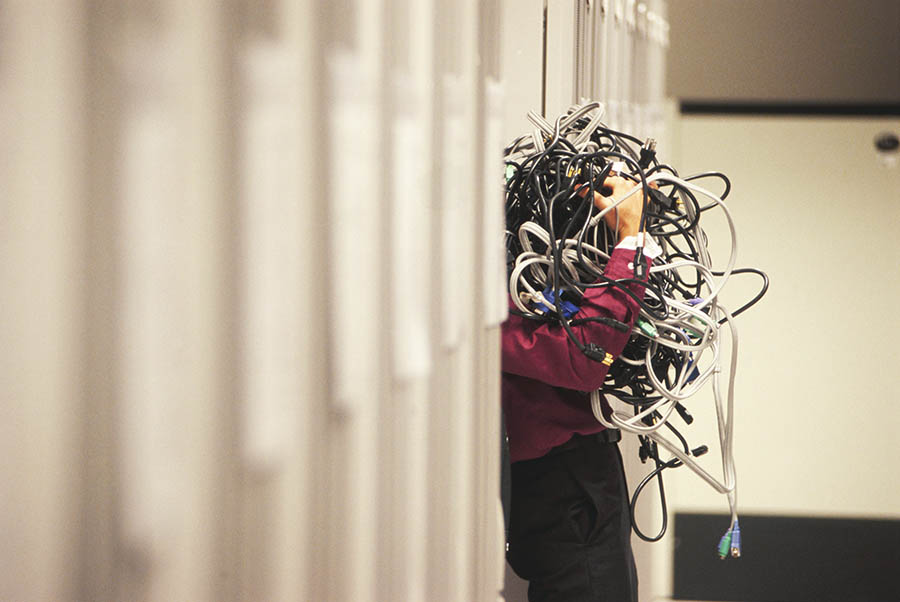
The problem begins with the sheer volume of alerts kicked up by tools used for threat monitoring and protection. Chronically short-staffed cybersecurity teams are hard pressed to handle them all, with many trapped in what one observer said amounts to a “Tinder for malicious behavior” — effectively swiping right or left through multitudes of potential threats. At the most basic level, in a security operations center (SOC), “That’s kind of the workflow, and it’s just a recipe for mistakes,” said security podcast host Patrick Gray.[i] Compounding the problem is the lack of integration among various threat monitoring tools, sending analysts toggling from dashboard to dashboard.
False positive security alerts make up one-third to one-half of all alerts, according to reports. While threat monitoring and protection tools are tuned to identify suspicious events, too often they end up generating false alerts on well-understood, safe activity — that staff must nevertheless spend time investigating.
Surveys Show Concerns Over Threat Monitoring and Protection
Surveys of cybersecurity professionals may differ at a detailed level but show a uniformly deep concern about how much time is wasted chasing false leads, distracting from proactive security efforts and raising the risk of missing real threats. Here are some of the findings on threat monitoring and protection:
- Volume and quality of alerts: The average SOC team fields over 11,000 alerts per day, mostly manually, according to Forrester’s 2020 State of Security Operations. Almost a third are false positives. Fewer than half of teams say they are able to address all their alerts in a single day, and over a quarter of alerts are ignored by analysts struggling to meet the workload.[ii]
- Time wasted on false positive alerts: The majority of respondents to another survey spend up to five hours a day investigating alerts. Nearly half of them usually find that half of their alerts were false positives.[iii]
- Risk increased by alerts: Security professionals surveyed in Dimensional Research’s 2020 State of SecOps and Automation report said the volume of alerts and false leads distracts from more important issues, increasing security risk. Seventy percent said overall security alert volumes have doubled in the past five years. Two-thirds said they waste time chasing false positives.[iv]
- Small teams’ woes: CISOs with smaller cybersecurity teams cite “too many alerts” among their top five pain points in the 2021 Survey of CISOs with Small Cyber Security Teams by Cynet, an IT staffing and recruiting firm. Nearly four out of five have a full-time team member chasing alerts. CISOs’ other biggest complaints are all related: overlapping technologies, too many dashboards, computing lag and, ultimately, an inability to view the full picture of an attack.[v]
False Positive Security Alerts Contribute to Skills Shortage
Few security teams can afford to waste time on false alerts. Due to an ongoing skills shortage in the industry, CISOs have difficulty hiring enough analysts to handle threat monitoring and protection. And in a vicious cycle, “alert fatigue” can lead to employee dissatisfaction and resignations. As a Forbes headline put it: “Cybersecurity Has a People Problem.”[vi]
What’s more, “It is evident that cybersecurity hiring and retention are not just a challenge for teams — they can have a very real impact on the security of their enterprises,” said Sandy Silk, director of IT Security Education & Consulting, Harvard University.[vii] Survey results on this topic include:
- Understaffing: Nearly two-thirds of security teams remain understaffed, according to the State of Cybersecurity 2020 from ISACA, a professional IT association. More than a third of those respondents that have taken three months or more to fill positions have suffered an increase in attacks.[viii]
- Employee dissatisfaction: Nearly a third of cybersecurity professionals cited an overwhelming workload as the most stressful aspect of their job, in the Enterprise Strategy Group’s Life and Times of Cybersecurity Professionals 2020, and about one-fifth cited “constant emergencies and disruptions that take me away from my primary tasks.” Nearly a third reported that they or a colleague had experienced significant personal issues as a result.[ix]
Technology Is Both Cause and Cure
Most agree that automation can help solve their problem with both alert volumes and the quality of alerts, though about two-thirds have only partially automated, according to the 2020 State of SecOps and Automation report. Those that have automated often face the challenge of managing multiple threat monitoring and protection tools.
Going forward, CISOs will increasingly use platforms that integrate threat data from multiple sources. Providers such as Mimecast, for example, not only block cyberattacks as a secure email service provider, but also offer integration with leading systems for security orchestration, automation and response (SOAR).
The Bottom Line
Technological solutions are on the way for the persistent problem of false positive security alerts. But for many companies, it’ll take time before these threat monitoring and protection solutions can be rolled out. In the meantime, the risk of cyberattacks and the employee dissatisfaction in cybersecurity teams remain higher for those who lag behind.
[ii] “The 2020 State of Security Operations,” Forrester
[iii] “The Impact of Security Alert Overload,” CriticalStart
[iv] “2020 State of SecOps and Automation,” Dimensional Research
[v] “2021 Survey of CISOs with Small Security Teams,” Cynet
[vi] “Cybersecurity Has A People Problem,” Forbes
[vii] “State of Cybersecurity 2020, Part 2,” ISACA
[viii] “State of Cybersecurity 2020, Part 2,” ISACA
[ix] “The Life and Times of Cybersecurity Professionals 2020,” Enterprise Strategy Group
Subscribe to Cyber Resilience Insights for more articles like these
Get all the latest news and cybersecurity industry analysis delivered right to your inbox
Sign up successful
Thank you for signing up to receive updates from our blog
We will be in touch!

