Cyber Resilience Insights Blog
The latest news and cybersecurity industry analysis at your fingertips.

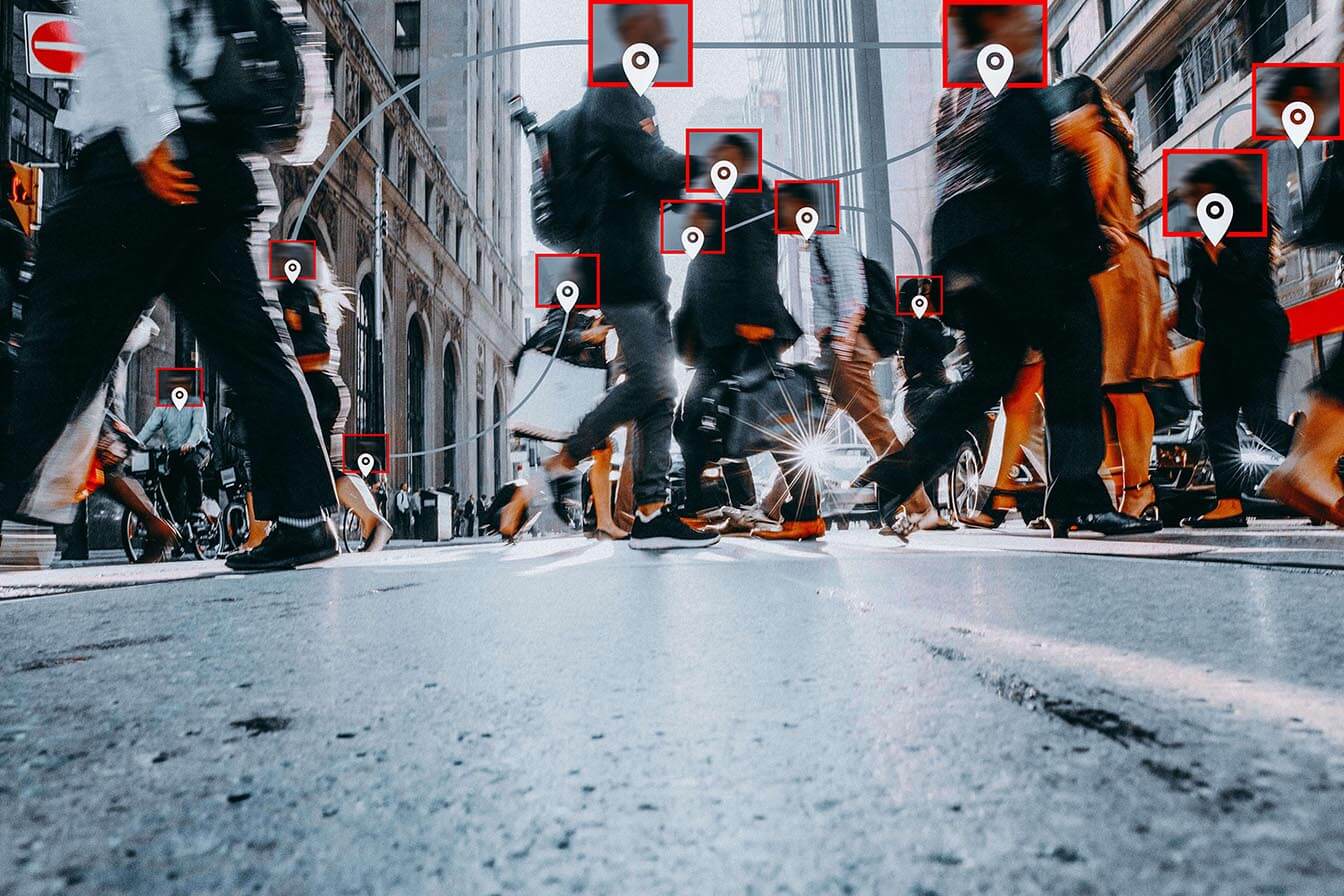
Unpacking the Microsoft Breach
The recent widely reported Microsoft breach should serve as a chilling reminder to organizations of all sizes and across all industries: No one, not even an industry giant, is immune to cyber attacks. While the incident is still under investigation and the attackers’ specific exploits have not been fully disclosed, Microsoft has confirmed publicly that password spraying was involved in the at...
Read moreExplore insights
Unfortunately we don't have any results matching your criteria, but you can try changing the selected filters above.
Special Collection
Securing Microsoft 365
Every day, organizations are exposed to unnecessary risk from attacks that could have been blocked; reliance on M365 protection alone may leave email vulnerable to attack. Here’s the key takeaway: Mass adoption of M365 has made it an irresistible target for cybercriminals. Explore this special collection of thought leadership about why it’s critical to secure M365.
Our Picks: Focus on Collaboration Security
Subscribe to Cyber Resilience Insights for more articles like these
Get all the latest news and cybersecurity industry analysis delivered right to your inbox
Sign up successful
Thank you for signing up to receive updates from our blog
We will be in touch!