FAQ sur le Phishing
Qu'est-ce qu'un courriel de phishing ?
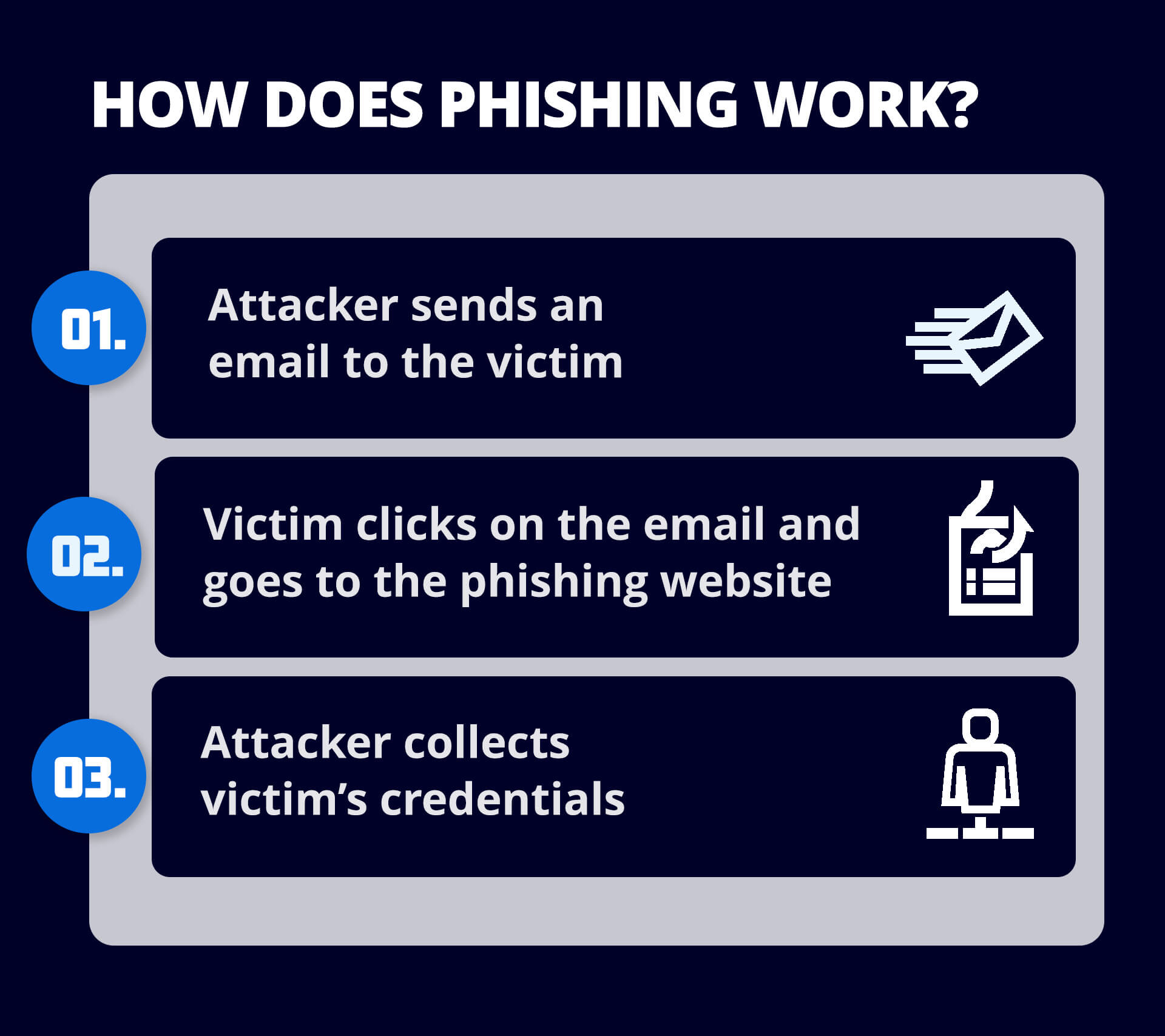
Un courriel de phishing est un courriel qui prétend provenir d'une organisation de confiance et qui tente d'inciter le destinataire à divulguer des informations sensibles telles que des mots de passe, des numéros de compte bancaire ou des détails de carte de crédit. Les courriels de Phishing peuvent également tenter d'inciter les utilisateurs à cliquer sur un lien qui téléchargera un malware sur leur ordinateur.
Comment repérer un courriel de phishing ?
Pour repérer un courriel de phishing, il faut être attentif aux détails qui ne concordent pas. Voici quelques signes à surveiller :
- "Adresses électroniques d'expéditeur suspectes : les courriels de Phishing proviennent souvent d'adresses qui ressemblent beaucoup à des adresses légitimes, mais qui présentent de légères variations, comme une lettre supplémentaire ou un domaine différent."
- Salutations génériques : les e-mails de phishing utilisent souvent des salutations génériques telles que "Cher client" au lieu de s'adresser au destinataire par son nom.
- Langage urgent ou menaçant : les courriels qui créent un sentiment d'urgence, vous avertissant d'un problème de compte ou d'une faille de sécurité, sont souvent conçus pour vous inciter à agir rapidement sans réfléchir.
- Mauvaise grammaire et fautes d'orthographe : de nombreux courriels de phishing contiennent des fautes d'orthographe et de grammaire évidentes que les organisations légitimes n'utiliseraient pas dans leurs communications.
- Liens ou pièces jointes suspects : Survolez toujours les liens avant de cliquer pour voir où ils mènent et évitez de télécharger des pièces jointes inattendues.
Comment bloquer un courriel de phishing ?
Même si un service de sécurité du courrier électronique tiers est en place, les utilisateurs doivent rester proactifs pour bloquer efficacement les emails de phishing. Voici comment :
- Restez vigilant: Soyez toujours prudent lorsque vous recevez des courriels inattendus, en particulier ceux qui vous demandent des informations personnelles ou financières. Vérifiez les signaux d'alerte tels qu'un langage inhabituel, des liens suspects ou des demandes d'action urgente.
- Vérifiez les coordonnées de l'expéditeur : Si un courriel vous semble suspect, ne vous fiez pas uniquement à son nom d'affichage. Vérifiez l'adresse électronique complète et, en cas de doute, contactez l'expéditeur par un autre canal pour vérifier la légitimité du message.
- Langage urgent ou menaçant: Les courriels qui créent un sentiment d'urgence, vous avertissant d'un problème de compte ou d'une faille de sécurité, sont souvent conçus pour vous inciter à agir rapidement sans réfléchir.
- Évitez de cliquer sur des liens ou de télécharger des pièces jointes: Ne cliquez jamais sur des liens ou ne téléchargez pas de pièces jointes provenant de courriels inconnus ou inattendus, même s'ils semblent légitimes. Survolez les liens pour prévisualiser l'URL et vous assurer qu'ils mènent à des sites de confiance.
- Marquez les courriels suspects comme étant du spam: Si un courriel suspect passe à travers vos filtres, marquez-le comme spam afin d'éviter les futurs messages de cet expéditeur. Cela peut également aider votre service de sécurité du courrier électronique à apprendre à mieux détecter ce type de courrier.
- Exploitez les fonctions avancées de votre service de sécurité de la messagerie: Votre service de sécurité pour la messagerie électronique recherche probablement les menaces de phishing en temps réel, en analysant les messages entrants à la recherche de liens dangereux, de pièces jointes malveillantes ou de domaines usurpés. Veillez à ce que des fonctions telles que la protection des URL et l'analyse des pièces jointes soient activées afin d'assurer une protection complète.
- Activez l'authentification multifactorielle (MFA): Si vous ou votre organisation n'avez pas mis en place l'authentification multifactorielle, il s'agit d'une étape cruciale pour se protéger contre le phishing. Même si les informations d'identification sont compromises, le MFA ajoute une couche supplémentaire de défense, empêchant l'accès non autorisé aux comptes.
- Mettez vos logiciels à jour: Assurez-vous que votre logiciel de sécurité, vos navigateurs et vos clients de messagerie sont à jour. De nombreuses tentatives de phishing exploitent les vulnérabilités de logiciels obsolètes. Des mises à jour régulières permettent donc de combler ces lacunes en matière de sécurité.
- Mettez en œuvre le DMARC (Domain-based Message Authentication, Reporting & Conformance): Si votre entreprise traite du courrier électronique, la mise en place de politiques DMARC contribuera à prévenir les tentatives d'usurpation d'identité et de phishing en garantissant que seuls des courriers électroniques légitimes sont envoyés à partir de votre domaine.
Qui sont les cibles des attaques de phishing ?
"Les attaques par Phishing peuvent viser n'importe qui, mais certains groupes sont plus vulnérables :"
- Les particuliers: Les utilisateurs quotidiens sont des cibles courantes, en particulier ceux qui sont moins habitués à reconnaître les tentatives de phishing.
- Les entreprises: Les entreprises, en particulier celles qui traitent des informations sensibles ou des transactions financières, sont fréquemment la cible d'attaques de spear phishing et de whale phishing.
- Les cadres: Les cadres de haut niveau, en particulier les PDG et les directeurs financiers, sont des cibles de choix pour les attaques de "whaling" car ils ont accès à d'importants actifs financiers et à des informations sensibles.
- Les employés des services sensibles: Les employés travaillant dans les services des ressources humaines, des finances ou de l'informatique sont souvent pris pour cible parce qu'ils traitent des informations critiques telles que les fiches de paie, les données personnelles ou les identifiants d'accès.
- Les clients des institutions financières: Les banques et les plateformes de paiement sont souvent usurpées dans des courriels de phishing visant à voler les informations relatives aux comptes des particuliers.
Qu'est-ce qu'un virus de phishing ?
Un virus de phishing est une forme de malware installé sur l'ordinateur d'un utilisateur dans le cadre d'une attaque de phishing. Le phishing est un type de cybercriminalité dans lequel les attaquants se font passer pour une entreprise fiable ou légitime afin de tromper un individu et de lui faire partager des informations telles que des numéros de compte bancaire, des détails de carte de crédit, des identifiants de connexion et d'autres données sensibles, et/ou de télécharger un virus de phishing sur l'ordinateur de l'utilisateur.
Pourquoi les attaques par phishing sont-elles couronnées de succès ?
Les attaques de phishing réussies reposent généralement sur plusieurs facteurs :
- Confiance : En semblant provenir d'une source que l'utilisateur connaît et en laquelle il a confiance, les attaques par phishing contournent toute suspicion à l'égard du courrier électronique entrant.
- La peur : de nombreuses attaques de phishing réussies incitent les utilisateurs à cliquer sur un lien en leur faisant croire qu'il y a un problème qui doit être résolu rapidement ou qu'il y aura des conséquences de la part d'une autorité supérieure ou d'un supérieur s'ils ne réagissent pas rapidement.
- Le manque de temps : Les attaquants savent que la plupart des utilisateurs manquent de temps et qu'ils veulent lire et répondre à un courriel le plus rapidement possible - ce qui fait qu'ils sont plus susceptibles de ne pas examiner attentivement son contenu.
- Le volume : Il est très peu coûteux d'organiser des attaques de phishing en envoyant de gros volumes de courrier électronique, et il suffit que quelques personnes "mordent à l'hameçon" pour que cela en vaille la peine.
- Les attaques de phishing sont de plus en plus sophistiquées et de plus en plus difficiles à repérer : Les attaques avancées telles que le spear-phishing et le whaling utilisent des techniques d'ingénierie sociale pour convaincre les destinataires qu'un courriel est légitime.
Comment prévenir le phishing ?
La prévention des attaques de phishing nécessite une approche multicouche de la cybersécurité.
- "Mettez en place une formation de sensibilisation à la sécurité pour les utilisateurs afin de les protéger contre l'erreur humaine - l'une des principales causes des failles de sécurité - en les aidant à repérer les signes de phishing."
- Mettez en œuvre l'authentification DMARC pour bloquer les courriels qui utilisent l'usurpation de domaine et le détournement de marque, qui sont courants dans le phishing.
- Déployer des programmes anti-phishing et anti-malware sur les terminaux et les réseaux.
- Encouragez les utilisateurs à exiger une authentification multifactorielle lorsqu'ils se connectent à leurs comptes.
Où dois-je signaler un cas de phishing ?
Si vous pensez avoir reçu un courriel de phishing, vous pouvez le transmettre à la Federal Trade Commission (FTC) à l'adresse suivante : spam@uce.gov. et au groupe de travail anti-hameçonnage (Anti-Phishing Working Group) à l'adresse reportphishing@apwg.org. Vous pouvez également signaler l'attaque à la FTC ( ftc.gov/complaint), à votre fournisseur de messagerie (Outlook ou Gmail, par exemple) et à l'entreprise dont l'identité est usurpée.