Money Mule Recruitment Scam Targets Higher Education
As students head back to campus to begin the school year, Mimecast’s Threat Center warns of a money mule scam targeting colleges and universities.

Key Points
- Money mule recruitment scams are nothing new for cybercriminals, who often use them for social engineering and credential theft.
- The new flavor of attack targets students in higher education, who may rely on their university to keep their emails safe from threat actors.
- Students falling for this money mule scam not only reveal personal information that could be used for nefarious purposes, but they also put the college or university they attend at risk.
A money mule is a person who knowingly or unknowingly transfers stolen money on behalf of others, usually through their bank account. The perpetrator of the attack offers a salary to the money mule to receive money into their bank account and transfer it to another account, obscuring the origin of the money and assuming the liability for the funds when the bank realizes the check is bad, or the money is stolen.
Work-from-home job scams, a common type of money mule recruitment, feign the offer of easy money for administrative tasks, such as printing labels and reshipping packages, buying gift cards, cashing checks and transferring money.
Continuing Scams in Continuing Education
Mimecast’s Threat Center has been tracking a Nigeria-based cybercriminal group posing as a consulting company; the group has been targeting college and university students with work-from-home job offers that aim to have them cash checks for a commission.
In this two-part operation, the scammers compromise student email accounts through phishing attacks, and then they send the job offer to the compromised student’s address book, which could include friends, professors, or other staff at the college or university. The job offer emails contain short URLs that redirect to a Google Form, and, as part of the application process, the recipient is asked to fill out a large amount of personal information. The targets are usually asked to provide an alternative, non-academic email address, giving the scammers access to other targets outside of the college or university.
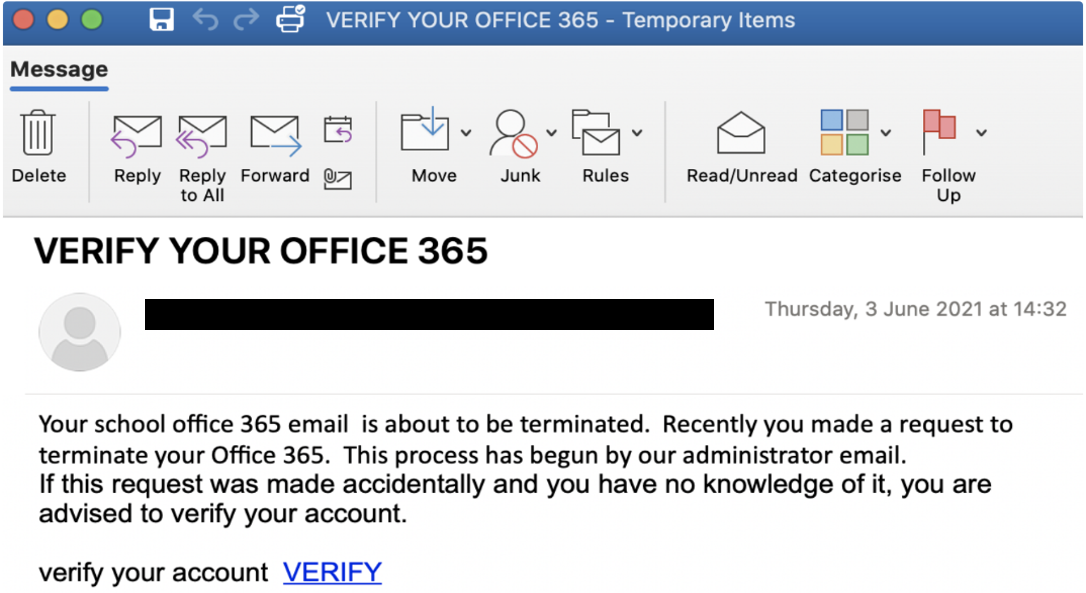
Part one of the threat actor’s operation, intro email.
Once the victim fills in the form revealing their personal information, the Nigeria-based scammers send a follow-up email providing details of the administrative tasks that come with the job, but the first responsibility always involves cashing checks. The email goes on to ask for confirmation of full name, occupation, physical address for receiving mail deliveries, a mobile number to receive texts, and whether the recipient knows how to make mobile deposits. These emails also use short URLs and redirect to a Google Form in the same style as the application form.
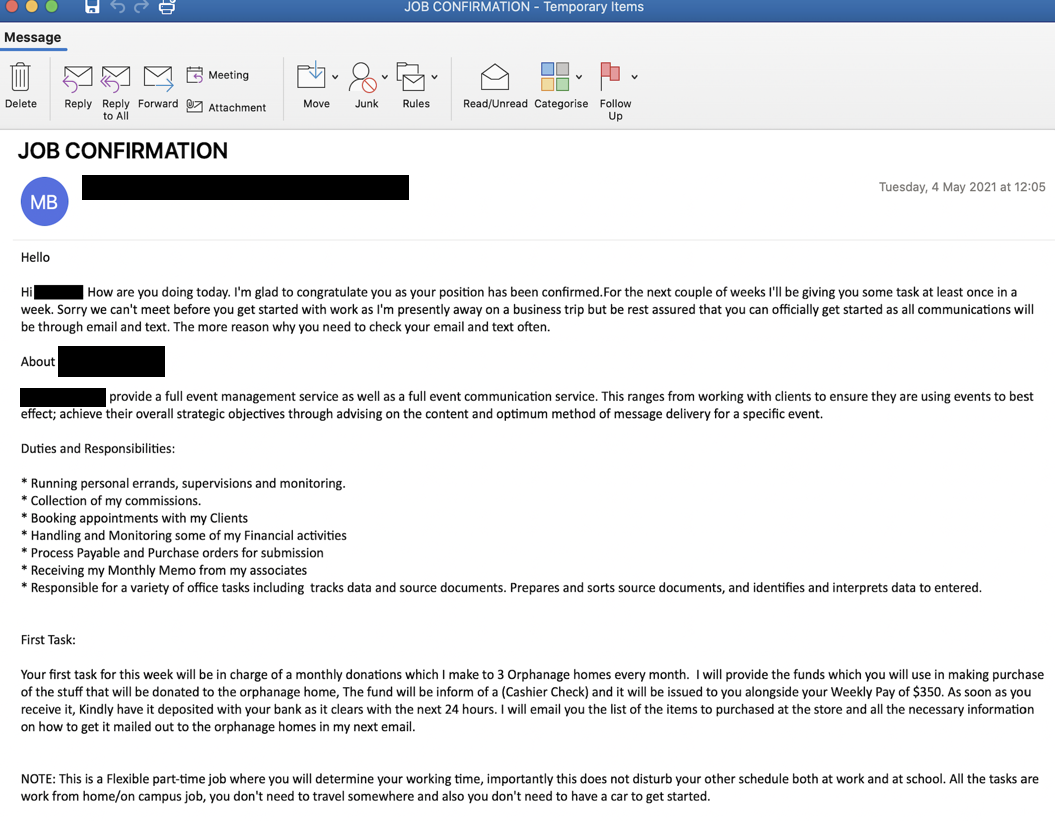
Part two, the follow-up email.
Higher Education Poses a Special Risk
In many large organizations today, these kinds of scams would raise flags among employees almost immediately. Unfortunately, students are a target-rich population for these schemes because many are struggling to pay for their education and they’re looking for quick or easy ways to make money. Another reason students make promising targets? Academic institutions often don’t put the same level of importance on securing student email accounts as they do protecting staff accounts – and cybercriminals know this.
In higher ed, students bring their own devices to leverage the open, accessible campus network. Yet, educational institutions struggle with tight budgets and limited IT resources, making it difficult to attract and retain experienced IT professionals. Additionally, security concerns are often a lower priority spend; decision makers tend to view IT investments as a high cost item yielding no significant ROI. They grapple with justifying the cost of security solutions, asking themselves how better security can lead to improved student outcomes. However, it’s clear there is a direct connection: students in higher education are targets for both simple and sophisticated scams that can put them and their institution at risk.
Scam Prevention
Students falling for this money mule scam not only reveal personal information that could be used for nefarious purposes, but they also put the institution they attend at risk. The information gathered in a money mule scam could be stored away and used in other sophisticated attacks that compromise the college or university network. In fact – while not the case in this scheme - past Threat Center research has demonstrated that at universities, proprietary research data, especially focused on new technology and defense, is extremely valuable to nation state hacker groups and state-sponsored hacking campaigns looking to steal and leverage cutting edge IP.
To mitigate the risk that students fall for money mule scams and other damaging cyberattacks, colleges and universities must:
- Offer engaging security awareness training at regular intervals. Students can be taught to detect red flags in scam emails, and avoid them.
- Consider using an email security solution that includes sophisticated algorithms that can detect impersonations, malicious emails and other anomalies. They must also put the same level of emphasis on securing student email accounts as the do on protecting staff accounts.
Additionally, while budgets in higher education institutions are unlikely to double overnight, they should ensure basic security fundamentals, such as patching, authentication protocols, etc., are in place.
The Bottom Line
Cybercriminals thrive on the same tried-and-true tactics with a new twist, whether it’s a global event like the Covid-19 pandemic, or the annual pilgrimage to college campuses, to dupe unsuspecting victims. According to Mimecast’s Threat Center, this particular money mule scam has continued for months and grown in earnest as students head back to colleges and universities, while the world still grapples with a pandemic and a sense of chaos. Colleges and universities must protect students, while students need to be more aware than ever.
Subscribe to Cyber Resilience Insights for more articles like these
Get all the latest news and cybersecurity industry analysis delivered right to your inbox
Sign up successful
Thank you for signing up to receive updates from our blog
We will be in touch!

