Phishing attacks explained
Phishing is one of the oldest forms of email attack, but it’s still prevalent in organizations of all sizes. It happens when fraudsters spam users online with emails; these emails sometimes promise prizes or threaten an account suspension, for example, then ask them to click on a link or go to a site to sort things out. Instead of winning a gift or reactivating that frozen credit card, users instead get their identities stolen or their computers infected with viruses.
How do phishing attacks work?
Phishing scams rely on tricking user into taking action — for example, in URL phishing, hackers want users to access a fake website and part with passwords and sensitive information. The site often asks the user to reset a password, reenter personal and credit information to validate an account, or download a “software update,” which is really malware in disguise.
Phishing attacks are becoming more sophisticated
Threats to enterprise security are constantly evolving and growing in complexity, and phishing threats are no exception.
In a phishing email, attackers masquerade as a reputable entity or a known person to dupe users into sharing important information like login credentials or account information. In a spear phishing email, attackers often pose as an individual within the recipient’s company, while the sender of a whale phishing email might impersonate the CEO or CFO and instruct the recipient to transfer money to a fraudulent account.
These kinds of phishing threats have been enormously successful. In fact, 91% of all hacking attacks today began with a phishing or spear phishing email. With each breach potentially costing millions in damage to business, productivity and reputation, organizations need sophisticated protection to guard against these ever-evolving attacks.
Different types of phishing techniques
Phishing remains the most popular form of cyberattack, and it has endured despite all efforts to fight it off. In recent years, phishing has evolved in new directions, such as targeted spear phishing, smishing (via text message) or vishing (using voicemail).
The impact of phishing attacks on businesses
The impact of phishing on businesses is harsh. According to annual reports by the Ponemon Institute, the average total cost of a data breach to a business, inclusive of damages like lost sales due to downtime, runs about $3.86 million. And as breaches get larger, so do the costs.
Defending against a phishing virus
A phishing virus typically starts with an email that seems to be from a legitimate source like a bank, a credit card company, a social website, an online payment processor or an IT administrator. The email directs the recipient to click on a link for a website that turns out to be malicious, and where the user is asked for some personal information like a passcode, credit card number, or account information. That info is then used to gain access to the user's accounts and to commit identity theft.
A spear-phishing virus is a more targeted phishing directed against a specific individual or role at the organization. This type of phishing virus attack uses social engineering techniques and information gathered about the individual to make the email more believable and increase the likelihood that the recipient will act on it.
Preventing phishing virus attacks requires sophisticated solutions that combine powerful email security technology with dynamic user awareness training. That's where Mimecast can help.
How Mimecast technology prevents a phishing email attack
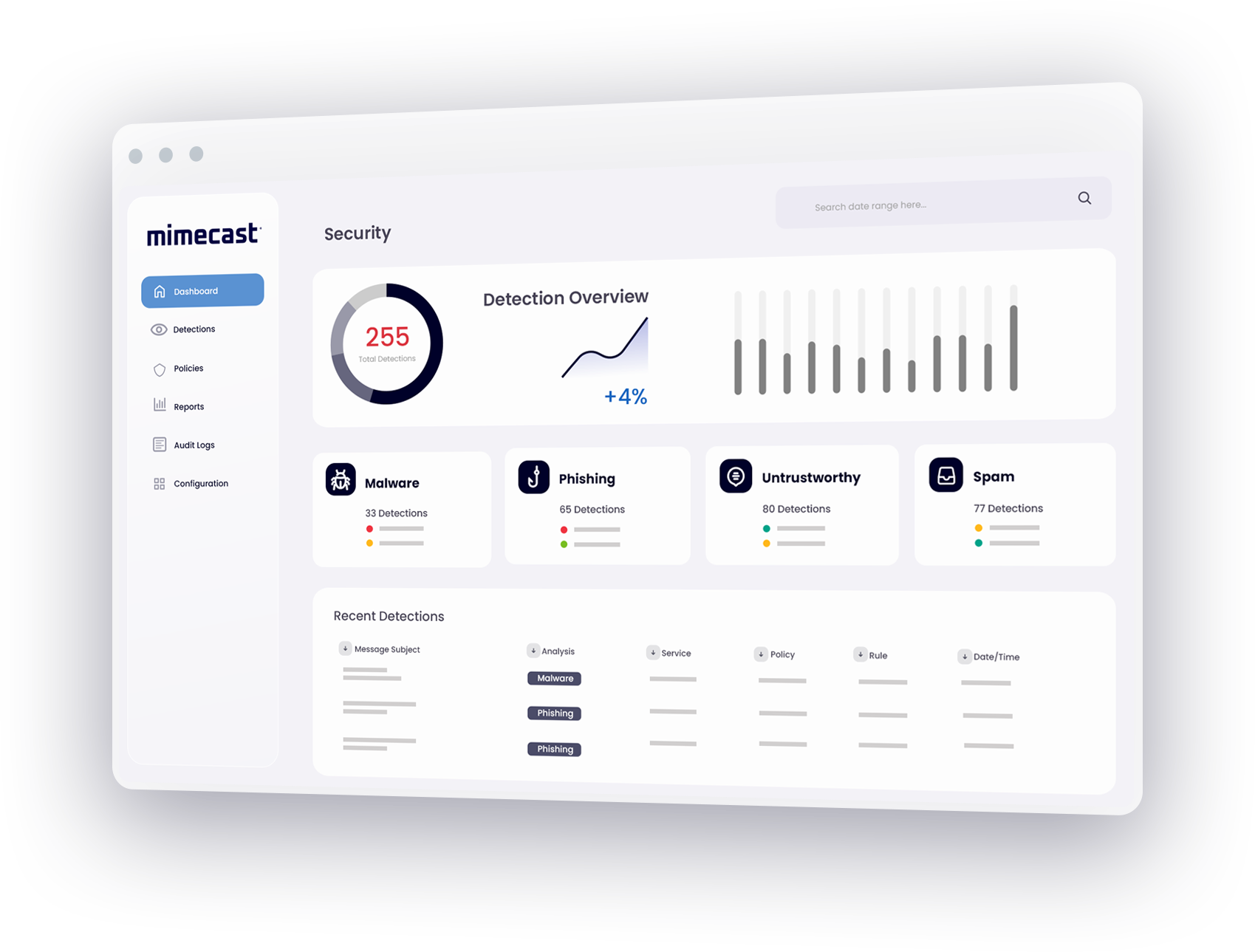
Mimecast Targeted Threat Protection defends against every type of phishing email threat.
Impersonation Protect identifies a whaling attack that uses social-engineering to trick employees into divulging confidential data or wiring funds to a fraudulent account. Mimecast scans all inbound emails in real-time, searching for specific signs of fraud in the header, domain and content of the message.
URL Protect prevents a phishing email attack by scanning all URLs within incoming and archived emails on every click and opening websites only if they have been determined to be safe.
Attachment Protect defends against weaponized attachments by sandboxing attachments and allowing only safe documents to be sent on to the user.
Benefits of Mimecast’s solution for a phishing attack
With Mimecast Targeted Threat Protection, organizations can:
- Prevent a phishing attack, spear phishing attack or whale phishing threat without the need for additional infrastructure or IT overhead.
- Add instant protection for all devices with no disruption to end-users.
- Activate the service quickly through Mimecast’s cloud platform.
- Improve insight with end-to-end, real-time threat analysis and granular reporting.
Learn more about stopping a phishing attack or CEO Fraud and about Mimecast’s solution for spam email protection and ransomware detection.
Phishing FAQs
What is a phishing email?
A phishing email is an email that pretends to be from a trusted organization and attempts to trick the recipient into divulging sensitive information like passwords, bank account numbers or credit card details. Phishing emails may also attempt to get users to click on a link that will download malware to their computer.
What is a phishing virus?
A phishing virus is a form of malware that is installed on a user’s computer as part of a phishing attack. Phishing is a type of cybercrime where attackers pose as a trusted or legitimate business to dupe an individual into sharing information such as bank account numbers, credit card details, login credentials and other sensitive data, and/or to download a phishing virus onto the user’s computer.
Why are phishing attacks successful?
Successful phishing attacks generally play on several factors:
- Trust: By appearing to originate from a source that the user knows and trusts, phishing attacks bypass any suspicion about incoming email.
- Fear: Many successful phishing attacks trick users into clicking a link by making them think there’s a problem that needs to be resolved quickly or that there will be consequences from a higher authority or a superior if they don’t respond quickly.
- Lack of time: Attackers know that most users are short on time and that they want to read and respond to an email as quickly as possible – which makes it more likely they won’t look closely at its content.
- Volume: It’s very inexpensive to mount phishing attacks by sending large volumes of email, and attackers only need a few people to “take the bait” to make it worth their while.
- Phishing attacks are increasingly sophisticated and more difficult to spot: Advanced attacks such as spear-phishing and whaling use social engineering techniques to convince recipients that an email is legitimate.
How to prevent phishing?
Preventing phishing attacks requires a multi-layered approach to cybersecurity.
- Implement security awareness training for users to defend against human error – one of the leading causes of security breaches – by helping users spot the signs of phishing
- Implement DMARC authentication to block emails that use domain spoofing and brand hijacking, which are common in phishing
- Deploy anti-phishing and anti-malware programs on endpoint devices and networks.
- Encourage users to require multi-factor authentication when logging into accounts.
Where should I report phishing?
If you believe you have received a phishing email, you can forward it to the Federal Trade Commission (FTC) at spam@uce.gov and to the Anti-Phishing Working Group at reportphishing@apwg.org. You may also report the attack to the FTC at ftc.gov/complaint, to your email provider (e.g., Outlook or Gmail) and to the actual company that the email is impersonating.